How not to give a hacker yourself outwit: a brief guide of the modern user
Technologies / / December 19, 2019
How not to give a hacker yourself outwit: a brief guide of the modern user
I am not a spy, and not a politician, in my computer and the phone do not have anything important. Do I need to hackers?
Carry out a special operation to kidnap one of your data is likely not going to. But their importance for attackers to underestimate still not worth it. Accounts banking applications, and even Instagram with three hundred subscribers or your home Wi-Fi-network - all this may be the goal of attackers.
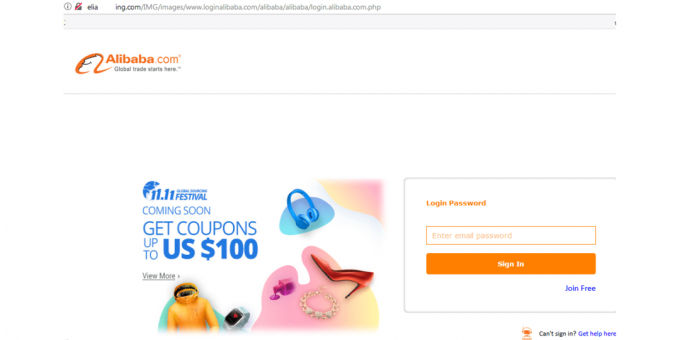
So-called phishing links that masquerade as real addresses of sites, not only actively sent in spam messages, but also occasionally appear in the top search results. All in the hope that someone will lead necessarily - will give hackers payment data or downloads malicious software.
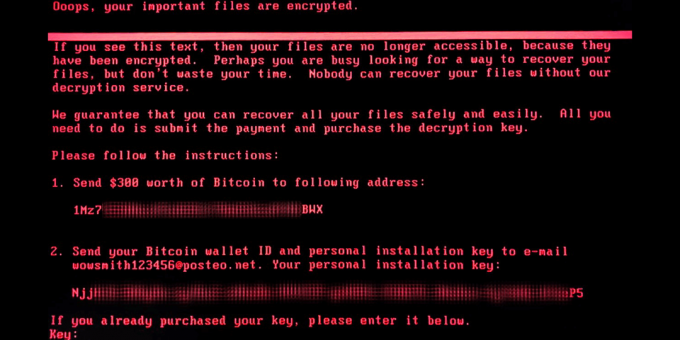
Recently, a large widespread program extortionists (which are only WannaCry and ExPetr). Their goal - to encrypt user data and to demand ransom for the decryption. The text of the message with the ransom can be completely different, and the cost is usually low, to prompt the user to pay.
Mobile devices represent a threat to banking Trojans - are malicious programs that allows attackers to gain access to logins and passwords and banking applications to steal user money. Pick up this infection can be in app stores or from the following link in a phishing SMS - so this year spread the Trojan Asacub.
In the arsenal of hackers every day there are new techniques and tricks. Therefore, any user needs to be aware of the modern means of protection.
And there are some clear rules that must be followed to avoid falling prey to scams?
The good news is that many of the threats can save quite simple hygiene rules on the Internet.
Keep your system and programs
Modern operating systems - it is an endless construction site. People use them, developers add features, identify vulnerabilities, add updates that eliminate the vulnerabilities, and so on ad infinitum. WannaCry already mentioned above would not have happened epidemic, if users set the time released in March update to Windows 10 with a corresponding patch.
Do not open links from strangers
Or even close if there is a suspicion that they broke. Look carefully in the sent URL: link to vkontatke.ru and odnoklossniki.ru - 100% indication of fraud. The same applies to the short address, passed through sokraschalki - people do not need to send a link to photos of cute seals or Anna Kournikova naked, wrapped through services vk.cc, tinyurl.com and goo.gl. The same rule works with the letters from banks and public services.
Pay attention to the file format
Do not be afraid of all the files with the extension EXE, but you need to know that the application can be any icon. Do not forget to check out the file format, setting the type of display icons "Table". If there is something that should not be an application has to EXE name - immediately remove.
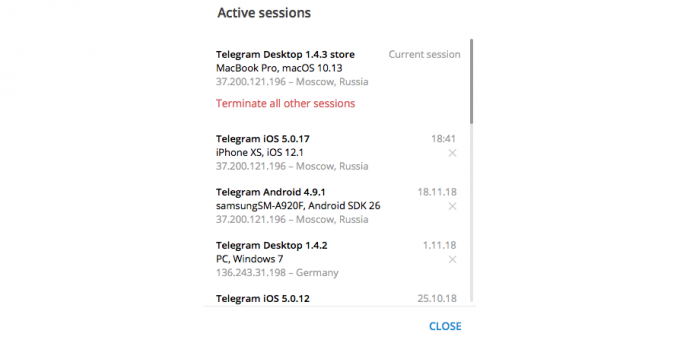
Check the sessions in instant messengers and social networks
The most popular services for communication, you can see who, when and from what device sign in to your account.
To see the history of sessions in "VKontakte", you need to go into the settings, select the section "Security" and click on the text "Show activity history." There you will see who, when and where to sign the social network under your login and password.
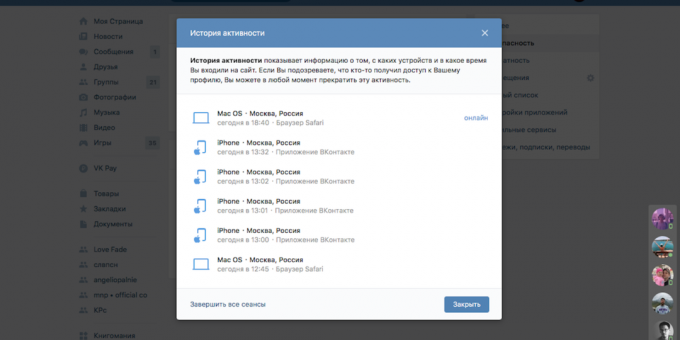
If you find someone else's device, or geolocation, click on the "End all sessions" and soon change the password account.
Do what you can, for example, in the Telegram, Facebook or Google.
Do not publish much information about themselves on social networks
Publish your phone number, you risk getting promotional mailings and phone calls, as well as phishing emails - such as SMS from fraudsters posing as bank staff. A large number of photos or videos to spread also not worth it: the theft of digital identity for a long time has passed from the movie scenes in real life. In addition, your property depicted in images, may be interested in the most common non-virtual thieves. We do not call just abandon the selfie with friends, but access to your accounts still need to limit - the appropriate settings for this exist in all social networks.
Set up two-factor authentication
Two-factor authentication - authorization, for which the system asks to log two types. For example, a password and a code from the SMS. This usually happens when you make a bank transfer via the app, but a similar function can be used in any service.
"Sewn" two-factor authentication have iOS, macOS, Instagram, Facebook, «VKontakte», Twitter, Google services, Telegram and WhatsApp. To access the applications without built-in authenticators can be used, for example, Authy and Google Authenticator.
Think already complex passwords
Use everything: different registers, letters, numbers, punctuation marks. And yes, the passwords should be long, ideally - 6-12 characters. Any simple arithmetic sequences, names and important dates. And yet the passwords for accounts in the various services should not be repeated.
To remember all this, you can come up with your encryption system and converted into a sequence of symbolic poems and children's rhymes. Better yet, use a special reliable password manager, which is a function of storing the bank card data and important images such as scans of passports.
Perform a complete check of devices now
Before you start doing the right thing, make sure that at the moment with all your devices well - perform a full scan systems for malware with a trusted anti-virus with the latest updates.
And what with your smartphone? There, too, the viruses?

If you have Android, it is possible (and also met on iOS malware). Each of the items in the previous chapter is relevant for mobile devices, but instead of Windows or macOS need to update your full-time operating system, and to be suspicious not to EXE, and to APK-files. In addition, there are a number of other rules.
Pick a reliable VPN-service
VPN - a kind of tunnel sandwiched between your device and the Internet, through which transferred your data. Everyone who is out of the tunnel, there is no access to information, and therefore, it can not be exploited.
Using a VPN to protect against the risk of hacker attacks when connected to an untested Wi-Fi-network, hide your data from fraudsters. This is useful if you, for example, pay for something on the map, connecting to public Wi-Fi-network.
There is one caveat: using a VPN, you give him the ability to track your traffic. That is why the question of choice of service must be approached very carefully, knowing, doubting and abandoning the free offers.
With careful use of public Wi-Fi-networks
The problem is that attackers can use public nezaparolennye Wi-Fi-network to steal personal user data. Closed networks can also be forged: the fraudster can learn the password from the Wi-Fi in a cafe or hotel create a fake network with the same name and password in order to steal personal information of unsuspecting customers.
If you are not sure of the safety of the connection and are not protected by the VPN, and Web log will still need at least do not use online banking and other important services. For them, better to use the mobile Internet on the operator.
Lock your smartphone screen
Without blocking the smartphone any person without any hacking skills can make your devaysom anything, it costs you only a distraction. PIN, pattern, fingerprint, face scan - it's enough to not be cleared by the attacker of your data in the most primitive way in the world.
Please note that no method of identification does not guarantee 100% protection - particularly vulnerable to the most budget Android-smartphone with the unlocking of the face. Some of them can be unlocked simply by showing your front camera image, so with them it is better to use Fingerprint or good old PIN code.
Do not install applications from untrusted sources
Only from official stores. And no doubt, firmware. Almost all applications require access to specific data, and there is no guarantee that the search engine found in the pirate APK-file will not dispose of them at the discretion of their developers.
And in the case of the Google Play should closely monitor the review and rating information from applications. Trojans are often hidden behind innocuous at first glance, applications, media players or flashlights. At the time, the Google Play was found 85 applications in which the attackers stole credentials of users "VKontakte".
Do not let the extra authorization applications
Notice what rights you are giving different applications. Especially suspicious concern those who ask for the right to process SMS messages. Flashlight obviously do not need access to the phone book or the microphone.
Back up systems and data
It will not protect you from data loss, but at least it will help them to recover, if malware will leave behind a scorched field. You can upload the files separately from your smartphone to cloud services or configure the backup feature in your smartphone - Android and many of its supporting shell.
But I already have some kind of antivirus. This is not enough?

If this is "some kind of anti-virus" - is likely enough. Especially if it is a random free program updates for which you have not watch.
Modern software for protection - it is not just antivirus. It is difficult from a technological point of view, a solution that takes care of the safety of all spheres of life of the Internet user.
Here's what can modern protection software.
- Protect against viruses, Trojans, and other threats cryptographers.
- Protect against spam and phishing.
- To ensure the security of bank card information when ordering food and shopping in online stores.
- To protect the user from spying via webcam.
- To work on different devices running Windows, Android and MacOS.
- Helping to generate strong passwords to protect user accounts from hacking.
- Make copies of important files to protect them from theft or loss by using the backup feature.
- Encrypt sensitive data user.
- Work without slowing down the system.
Dozens of features rarely come in handy at one point, so the modern software for data protection and should be more time to adapt to different conditions. For example, at home you may need detection function strangers in Wi-Fi-network, but use a VPN in their room more often there is no need. If you use the Internet at the cafe - just the opposite.
Today's software is very far gone from the antivirus, which we remember from the times of pirate collections "Golden Software 2002". Developers also sit on the internet and know how to defend against current threats. So if you think that in 15 years nothing has changed, and, for example, "Kaspersky" - this is only the tray icon, which publishes the frightening sound of pigs, it is, to put it mildly, not quite.
Well, I understand everything. You advise any convenient option?
Yes. For example, the solution Kaspersky Security Cloud can be used on both the computer and the smartphone, also on different platforms: Windows, macOS, Android or iOS. It will protect your device from all or almost all, that threatens the security of your data. This solution with the technology of adaptive protection time will tell, for example, an unknown device is connected to your home Wi-Fi-network, will make the process safer online shopping, check the reliability of your passwords and ensure the safety of data when connecting to public Wi-Fi-networks.
Version of Kaspersky Security Cloud Personal will cost 2990 rubles per year by connecting three devices, and 3990 rubles - if you connect five. Kaspersky Security Cloud Family with enhanced parental controls and flexible connection of up to 20 devices will cost 5990 rubles per year. And, you can download a trial version - 30 days free of charge.
Try Kaspersky Security Cloud



